Inside the ThreatVeil Decision Engine: From Signals to Proof
Why most security tools stop halfway
2/5/20261 min read
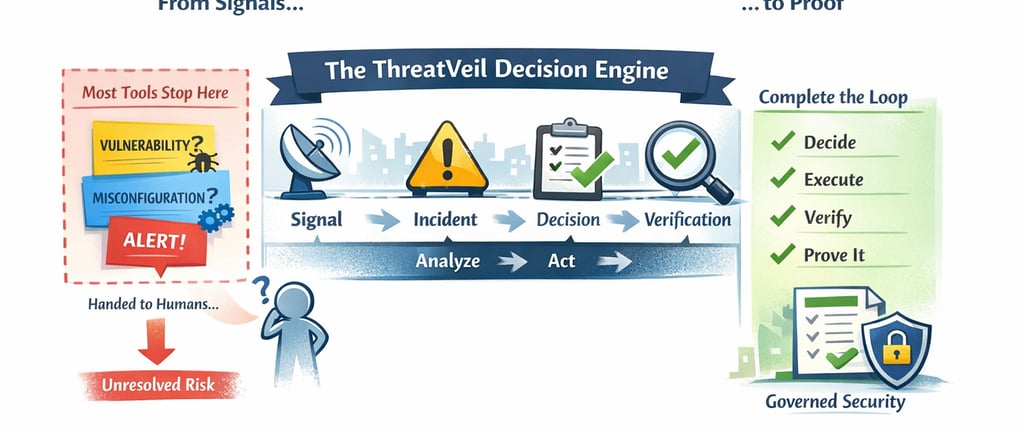

Most tools stop after detection:
“Here’s a vulnerability”
“Here’s a misconfiguration”
“Here’s an alert”
Then they hand the problem to humans and hope for the best.
But real security requires closure:
deciding what to do
executing safely
verifying results
The ThreatVeil Decision Engine was built to own that entire loop.
The ThreatVeil decision pipeline
ThreatVeil operates on a strict, auditable contract:
Signal → Incident → Decision → Verification
Here’s what makes it different.
1. Signals are evidence, not noise
Every signal entering ThreatVeil carries:
source
confidence
freshness
asset context
evidence references
No anonymous alerts.
No black boxes.
2. Incidents create meaning
Signals are correlated into incidents:
grouped by asset, identity, repo, or system
ordered into timelines
explained in plain language
This answers:
“What’s actually happening?”
3. Decisions are explicit and logged
Each incident results in a decision:
what action is recommended
why it matters
what outcome is expected
how success will be verified
Decisions are written to a ledger, becoming a system-of-record.
4. Verification is mandatory
ThreatVeil doesn’t assume remediation worked.
It verifies:
rescans
telemetry confirmation
configuration validation
signal disappearance
If verification fails, the decision stays open.
Why AI doesn’t make the decisions
ThreatVeil uses AI — but very deliberately.
AI is allowed to:
explain incidents
summarize rationale
generate executive narratives
suggest remediation steps
AI is not allowed to:
rank risk
choose priorities
execute destructive actions
Trust requires determinism.
The outcome: security with proof
The result is security that can say:
“We made this decision”
“For this reason”
“At this time”
“And here is the evidence it worked”
That’s not just better security.
That’s governable security.
